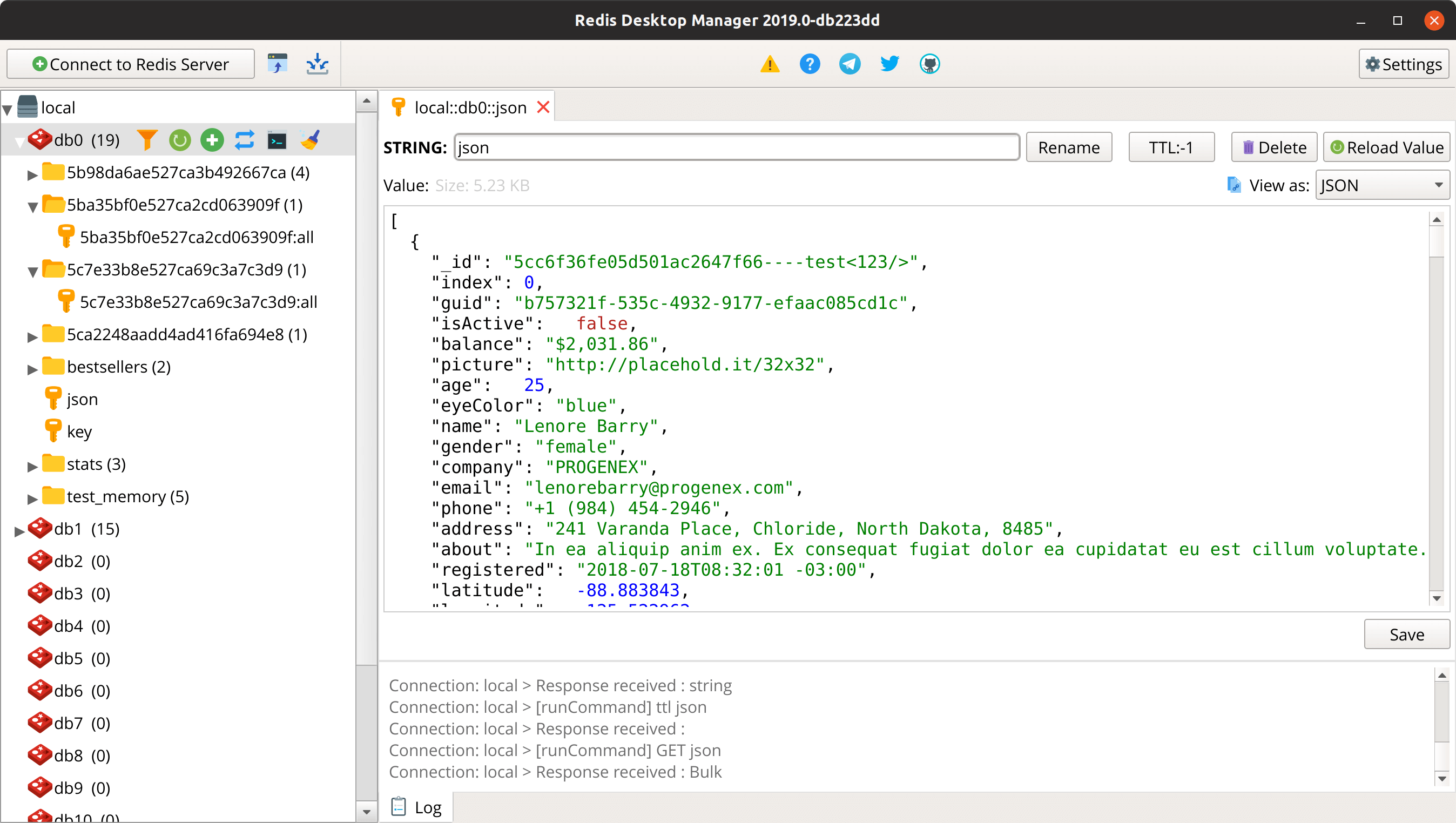
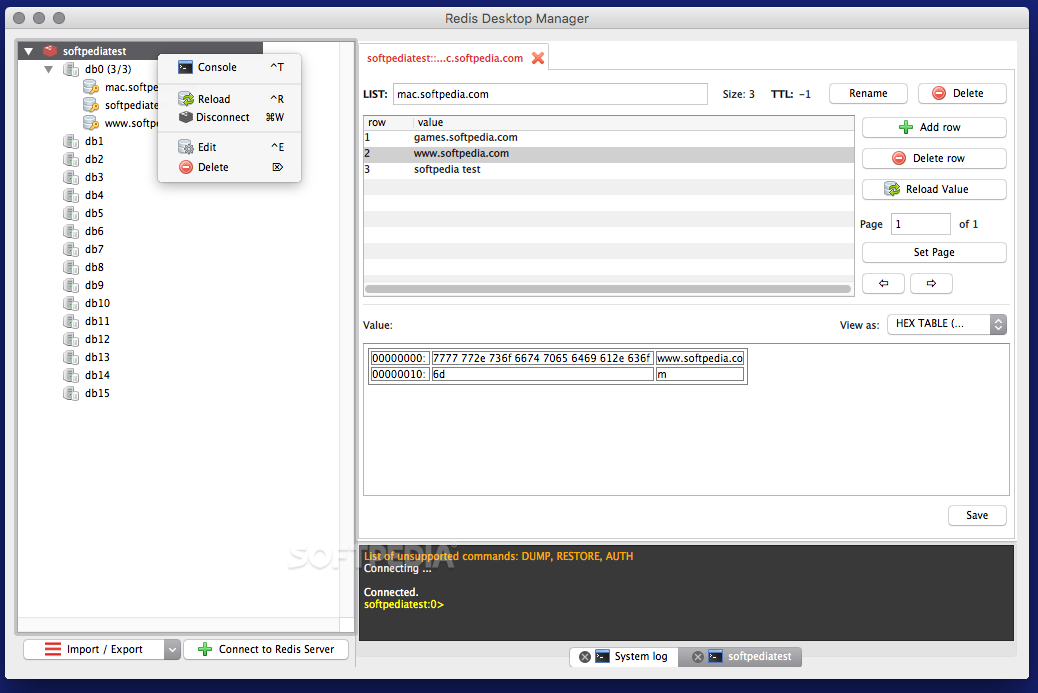
Download RDM - GUI for Redis ® for macOS 10.14.0 or later and enjoy it on your Mac. RDM offers you an easy-to-use GUI to access your Redis ® databases and perform some basic operations:. View keys as a tree. CRUD keys. Analyse memory usage for entire DB or for selected namespace in tree-view (redis-server = 4.0 is required). List currently connected clients, opened Pub/Sub. Redis GUI Client for Mac. Redis GUI Client for Mac. RedisInsight is the successor to RDBTools! RDBTools will reach EOL on 31st December 2019. Get RedisInsight here! The 2020.5.137 version of Redis Desktop Manager for Mac is available as a free download on our software library. This free Mac application was originally developed by Igor Malinovskiy. The file size of the latest downloadable installation package is 9.2 MB. Our antivirus scan shows that this Mac.
FastoRedis (fork of FastoNoSQL) - is a cross-platform open source Redis management tool (i.e. It put the same engine that powers Redis's redis-cli shell. Everything you can write in redis-cli shell - you can write in Fastoredis! Our program works on the most amount of Linux systems, also on Windows, Mac OS X, FreeBSD and Android platforms.
In this article, I will explain how to secure your Redis databases using SSL (Secure Sockets Layer). In production, it is a good practice to use SSL to protect the data that are moving between various computers (client applications and Redis servers). Transport Level Security (TLS) guarantees that only allowed applications/computers are connected to the database, and also that data is not viewed or altered by a middle man process.

You can secure the connections between your client applications and Redis cluster using:
- One-Way SSL: the client (your application) get the certificate from the server (Redis cluster), validate it, and then all communications are encrypted
- Two-Way SSL: (aka mutual SSL) here both the client and the server authenticate each other and validate that both ends are trusted.
In this article, I will focus on the Two-Way SSL, and using Redis Enterprise.
Prerequisites:
- A Redis Enterprise 5.4.x database, (my database is protected by the password
secretdb01, and listening on port12000) redis-clito run basic commands- Python, Node, and Java installed if you want to test various languages.
Simple Test
Let’s make sure that the database is available:
This should print the Server information.
1- Get the Certificate from Redis Cluster
You have access to the Redis Enterprise Cluster, you go to one of the nodes to retrieve the certificate (that is a self-generated one by default).
The cluster certificate is located at: /etc/opt/redislabs/proxy_cert.pem.
You have to copy it on each client machine; note that once it is done you can use this certificate to connect using “One-Way SSL”, but not the purpose of this article.
In my demonstration I am using Docker and copy the certificate using this command from my host:
2- Generate a New Client Certificate
Using the Two-Way SSL you need to have a certificate for the client that will be used by Redis database proxy to trust the client.
In this article I will use a self-signed certificate using OpenSSL, in this example, we are creating a certificate for an application named app_001.
You can create as many certificates as you want, or reuse this one for all servers/applications.
Open a terminal and run the following commands:
This command generate a new client key (client_key_001.pem) and certificate (client_cert_001.pem) with no passphrase.
3- Configure the Redis Database
The next step is to take the certificate and add it to the database you want to protect.
Let’s copy the certificate and paste it into the Redis Enterprise Web Console.
Copy the certificate in your clipboard:
Mac:
Linux:
Windows:
Go to the Redis Enterprise Admin Web Console and enable TLS on your database:
- Edit the database configuration
- Check TLS
- Select “Require TLS for All communications”
- Check “Enforce client authentication”
- Paste the certificate in the text area
- Click the Save button to save the certificate
- Click the Update button to save the configuration.
The database is now protected, and it is mandatory to use the SSL certificate to connect to it.
Redis Client Mac Os
4- Connect to the Database using the Certificate
In all following examples, I am using a “self-signed” certificate, so I do not check the validity of the hostname.You should adapt the connections/TLS information based on your certificate configuration.
4.1 Using Redis-CLI
To connect to a SSL protected database using redis-cli you have to use stunnel.
Create a stunnel.conf file with the following content:
Start stunnel using the command
This will start a process that listen to port 6380 and used as a proxy to the Redis Enterprise database on port 12000.
4.2 Using Python
Using Python, you have to set the SSL connection parameters:
More information in the documentation “Using Redis with Python”.
4.3 Using Node.JS
For Node Redis, use the TLS library to configure the client connection:
More information in the documentation “Using Redis with Node.js”.
4.4 Using Java
In Java, to be able to connect using SSL, you have to install all the certificates in the Java environment using the keytool utility.
Create a keystore file that stores the key and certificate you have created earlier:
As you can see the keystore is used to store the credentials associated with you client; it will be used later with the -javax.net.ssl.keyStore system property in the Java application.
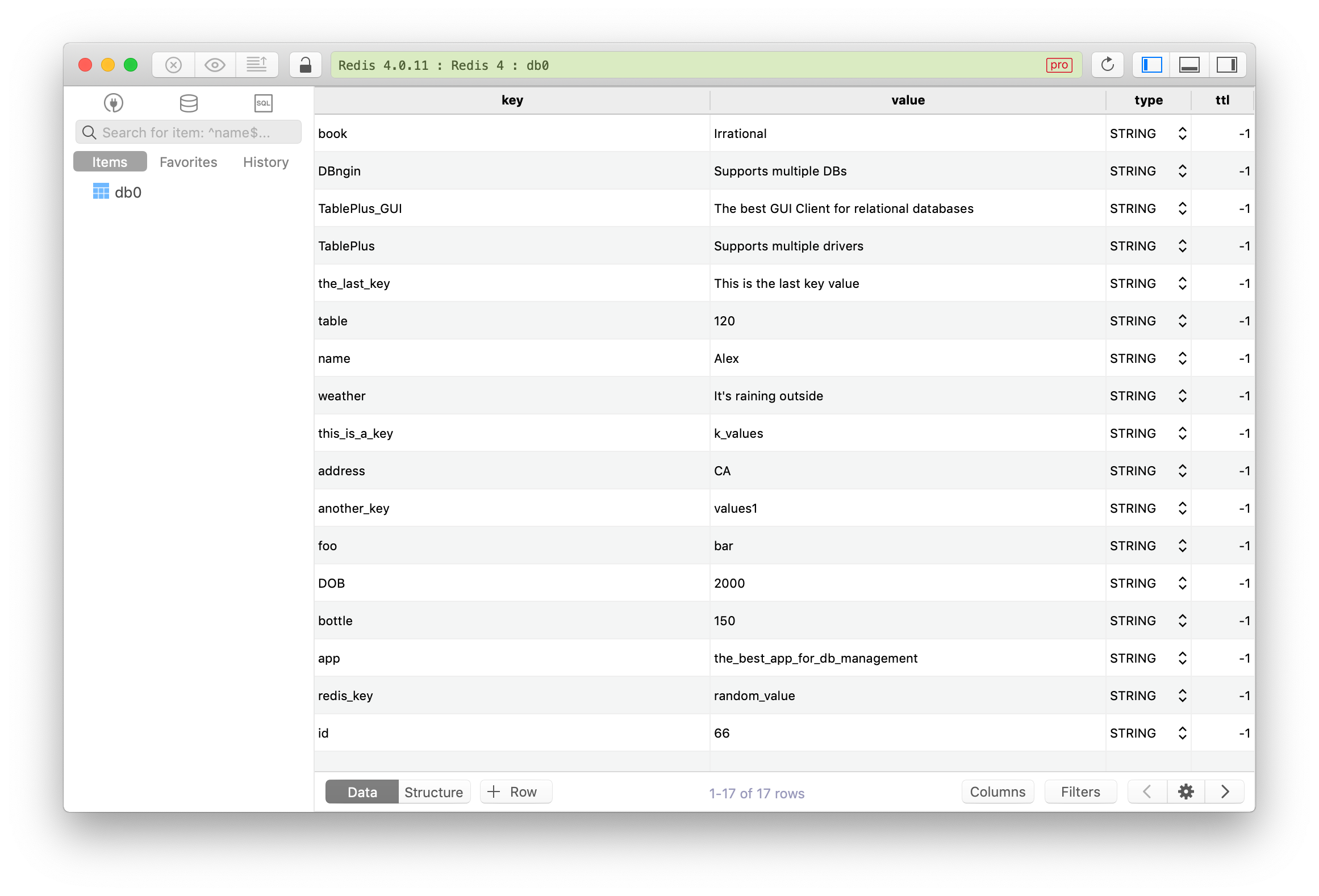
Free Redis Gui Client
In addition to the keys tore, you also have to create a trust store, that is used to store other credentials for example in our case the redis cluster certificate.
Create a trust store file and add the Redis cluster certificate to it
The trustore will be used later with the -javax.net.ssl.trustStore system property in the Java application.
You can now run the Java application with the following environment variables:
For this example and simplicity, I will hard code these property in the Java code itself:
- line 8-12, the system environment variables are set to point to the keystore and trust store (this should be externalized)
- line 14, the Redis URL start with
redisswith 2 s to indicate that the connection should be encrypted - line 17, set the database password
More information in the documentation “Using Redis with Java”.
Conclusion
In this article, you have learned how to:
- retrieve the Redis Server certificate
- generate a client certificate
- protect your database to enforce transport level security (TLS) with 2 ways authentication
- connect to the database from
redis-cli, Python, Node and Java